Overview
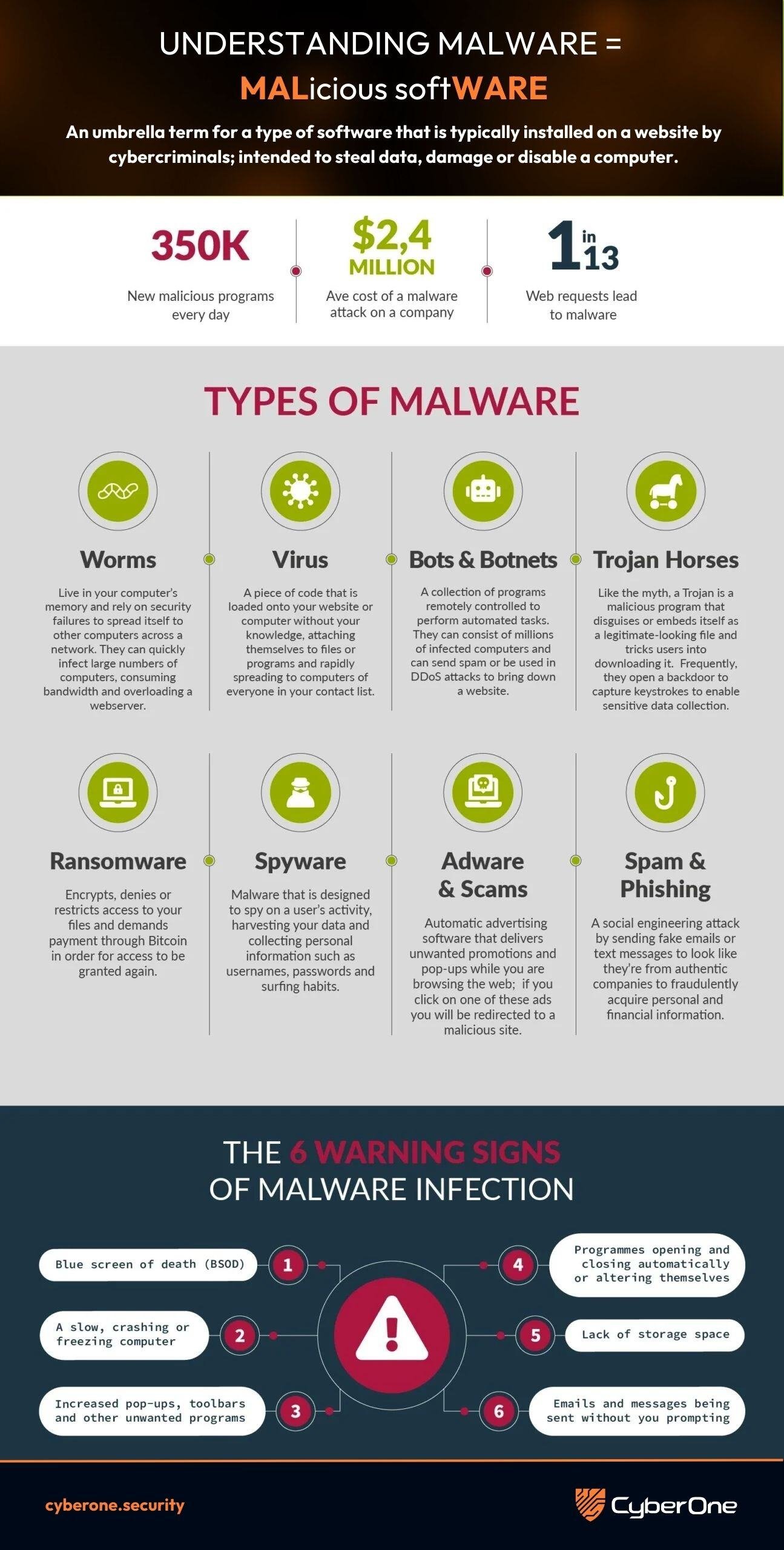
The threat landscape is witnessing a sharp rise in modular loaders—malware designed to establish initial footholds and enable follow-on payloads. CastleLoader, a relatively new but rapidly evolving loader, has become the latest tool of choice for four separate threat clusters. These clusters are believed to be connected to or serviced by GrayBravo—a threat group known for running a sophisticated Malware-as-a-Service (MaaS) operation.
CastleLoader’s expansion marks a significant shift toward scalable, service-based cybercrime infrastructure, allowing multiple actors to share the same delivery platform while deploying customized malicious payloads.

What is CastleLoader?
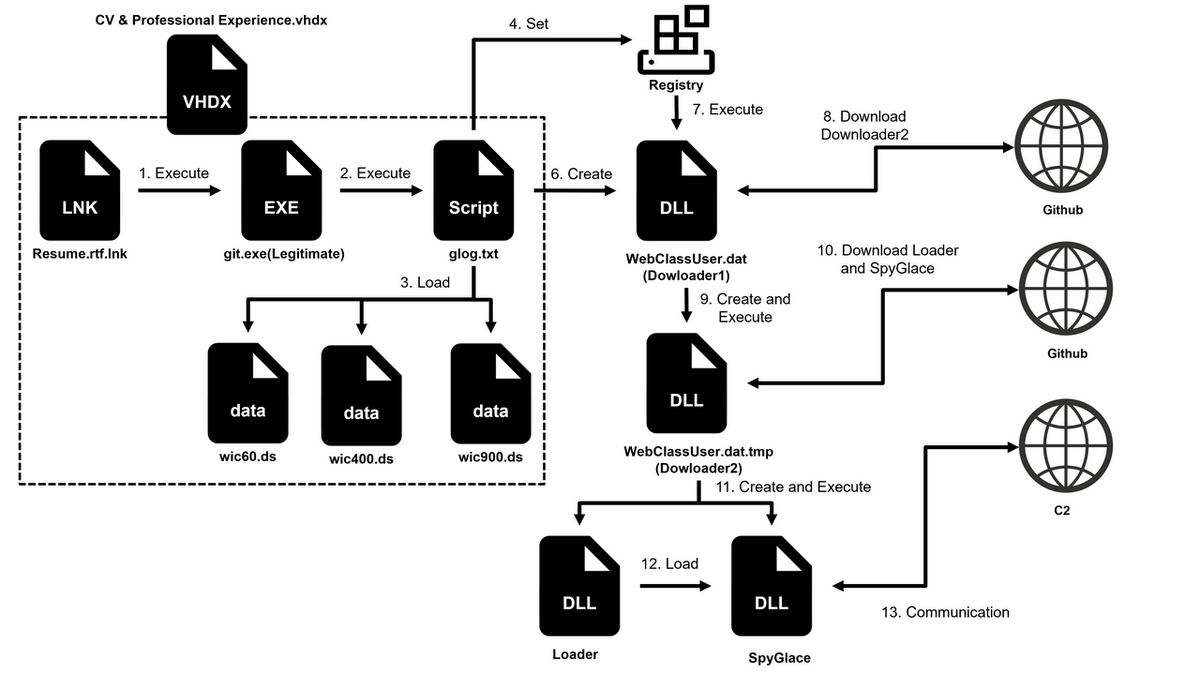
CastleLoader is a stealthy, multi-stage malware loader built for:
- Initial access
- Payload delivery
- Persistence
- Infrastructure diversification
Its key features include:
- Fileless execution to avoid detection
- Encrypted command-and-control (C2) channels
- Modular plugin system allowing threat actors to load custom tools
- Anti-analysis capabilities (sandbox evasion, debugger checks)

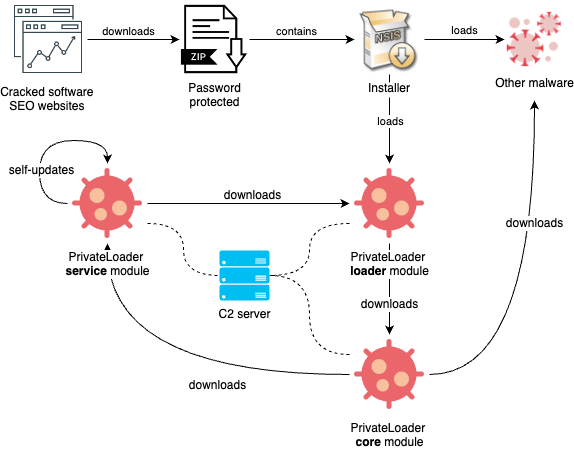
Because of its flexible architecture, CastleLoader is increasingly being rented out to other groups, similar to how Emotet, Qakbot, and IcedID operated before takedown attempts.
Who is GrayBravo?
GrayBravo (sometimes associated with state-aligned and financially motivated hybrid TTPs) is a threat actor known for:
- Developing malware families for resale or leasing
- Running resilient distributed C2 infrastructure
- Offering loader-based access as part of its MaaS ecosystem
- Reinvesting revenue to expand infrastructure and obfuscation layers
The growth of GrayBravo’s service infrastructure indicates that CastleLoader is now moving from a single-actor tool to a shared platform supporting multiple campaigns.
The Four Threat Clusters Using CastleLoader
Below are the four identified clusters, each displaying unique tactics, techniques, and objectives while leveraging the same loader.
Cluster 1: Credential Theft & Initial Access Brokers (IABs)
Objectives
- Harvest enterprise credentials
- Sell network access on dark-web markets
- Serve ransomware affiliates
Tactics
- Phishing emails with malicious attachments
- CastleLoader used to install credential dumpers (Mimikatz variants)
- Low-noise persistence via scheduled tasks
Impact
This cluster fuels ransomware ecosystems by providing ready-made access to corporate environments.
Cluster 2: Financially Motivated Banking Malware Operators
Objectives
- Steal online banking information
- Inject web-based stealers
- Perform session hijacking
Tactics
- CastleLoader deploys banking trojans (e.g., Gozi variants, custom stealers)
- Man-in-the-browser scripts delivered post-injection
- Use of proxy-based C2 for transaction manipulation
Impact
Targets retail banking customers, SMEs, and financial institutions.
Cluster 3: Espionage-Driven APT Operations
Objectives
- Long-term unauthorized access
- Data exfiltration (IPs, documents, R&D secrets)
- Covert surveillance
Tactics
- CastleLoader as the entry point for lightweight backdoors
- Encrypted lateral movement tools
- Use of multi-tier C2 for stealth and redundancy
Impact
High-risk campaigns targeting government, telecom, and defense.
Cluster 4: Botnet & Distributed Attack Operators
Objectives
- Expand botnet size
- Conduct DDoS attacks
- Sell botnet rental services
Tactics
- CastleLoader installs bot agents on compromised hosts
- Rotating C2 domains to maintain uptime
- Payload updates delivered via CastleLoader plugins
Impact
These operators increase the global DDoS attack capacity and distribute malicious traffic.
Why CastleLoader Is Becoming Popular

1. Highly modular design
Threat actors can attach custom payloads like LEGO blocks.
2. Strong anti-detection engineering
Obfuscation, encryption, and memory-only execution make it resilient.
3. MaaS scalability
GrayBravo’s infrastructure allows multiple clusters to run parallel campaigns.
4. Regular code updates
Frequent version releases help bypass YARA rules and signature-based defenses.
GrayBravo’s Expanding Malware Service Infrastructure
GrayBravo is now investing in:
- Fast-flux DNS networks for resilient C2
- Cryptocurrency-based affiliate payments
- Customizable loader configurations per client
- Redirection frameworks to hide real origins
- Decoy infrastructure to mislead defenders
This expansion mirrors the evolution of major historical botnet-loaders like:
- Emotet
- TrickBot
- Qakbot
CastleLoader may be on its way to becoming the backbone of multiple cybercrime ecosystems.
Defensive Recommendations
1. Strengthen Email & Endpoint Detection
- Block macros and suspicious attachment types
- Deploy advanced EDR with memory scanning
2. Detect Loader-Like Behavior
Look for:
- Unusual PowerShell execution
- Unexpected registry persistence keys
- Outbound encrypted traffic to unknown domains
3. Threat Hunting Indicators
Focus on:
- DNS anomaly detection
- Connections to recently registered domains
- Failed application whitelisting attempts
4. Patch & Harden Systems
- Apply OS, browser, and plugin updates
- Limit admin privileges
Conclusion
CastleLoader’s rise—supported by GrayBravo’s growing malware-as-a-service ecosystem—signals a new phase of shared cybercrime infrastructure. With four different threat clusters already leveraging it for diverse motives, defenders must expect rapid evolution, stronger evasive techniques, and increased campaign frequency.